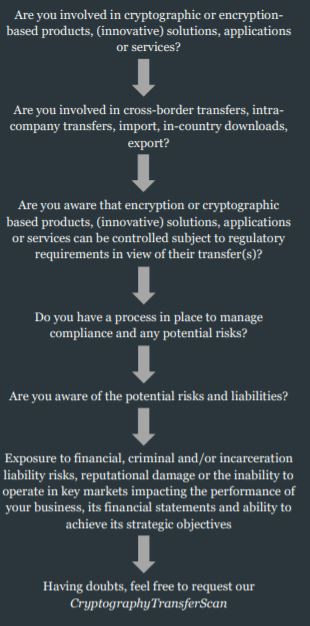
Cryptography driven technology and software have become part of our daily routine found in numerous products, applications, (security) solutions and services. At the same time, sharing and transferring such software and technology is not without any measure of constraint. Numerous governments monitor and control transfer of cryptography for (inter)national security, national cryptography, trade or foreign policy interests and objectives. Due to the rise of the digital economy, digital transformation and telecommuting, this is becoming an area of increasing regulatory interest and enforcement. Any non-compliance can lead to severe penalties, even personal liability.
What type of transfer?
Each country has its own national cryptography policy and regulatory framework controlling certain type of transfer activity.
Types of transfers being regulated can involve any of the following activities:
- Supply
- Import
- In-country transfer and/or download
- Intra-EU Member States transfer
- Export
The national regulatory frameworks can control tangible as well as intangible transfers (e.g. electronic transfers such as e-mails, cloud computing, open source community, etc.).
Different countries, different rules
The legal and regulatory requirements regarding cryptography transfers differ per country.
Do you have a process in place to manage compliance and any potential risks?
For each country, however, the main starting point is to have clearly identified whether your product, application, solution or service is using cryptography (or e.g. embeds activation of encryption functions) in order to be able to check the applicability and if so mandatory compliance regarding the transfer regulatory requirement in the country concerned.
In some countries, the scope and compliance regulatory requirements are moderate while, in other countries, burdensome and complex. We have extensive experience dealing with various governmental administrations having built strong relationships over the past years.
Time to ask yourself…
Our key experience:
- Advising a multinational computer software and technology developer regarding the applicability and enforcement of import and export encryption controls in view of licensing, cross-border asset purchase agreements, software licensing agreements and day-to-day cross-border sales and transfers of encryption software and related source code to various countries. We incorporated encryption controls compliance manuals, evaluated contractual clauses as well as performed a risk and liability assessment of past sales, supplies and transfers regarding encrypted products.
- Advising an American multinational investment bank and financial services company regarding encryption controls and related licensing for the import of encryption based mobile authenticators in various third countries.
- Advising a global artificial intelligence company regarding the import encryption controls for its platform software for artificial intelligence and machine learning technologies.
- Advising an international cyber security and privacy company regarding encryption controls regarding of its secure storage mobile applications as well as submitting successful voluntary selfdisclosure regarding past violations to the competent authority.