KEY TAKEAWAYS
- The regulatory landscape is congested, with varied obligations that are relevant to cyber security incidents administered by a patchwork of regulators
- The number of cyber security related regulations is increasing.
- At the same time, we are seeing a shift away from government and regulators viewing the attacked as the victim. With this comes increasing exposure to the risk that regulators will take enforcement action against businesses that fail to take adequate steps to prevent cyber-attacks and data breaches.
- These trends are likely to continue. Businesses should keep an eye on overseas developments to remain ahead of the curve.
- Enforcement action can lead to significant penalties and reputational harm. To minimise the risk of regulatory enforcement action, businesses must be proactive in complying with their cyber security obligations.
WHO REGULATES CYBER SECURITY?
The regulatory landscape is congested, with varied obligations that are relevant to cyber security incidents administered by a patchwork of regulators
Australia does not have a unified regulatory framework for managing cyber risks or cyber security incidents.
Instead, cyber security regulations are divided among a mix of sector and/or conduct specific obligations.
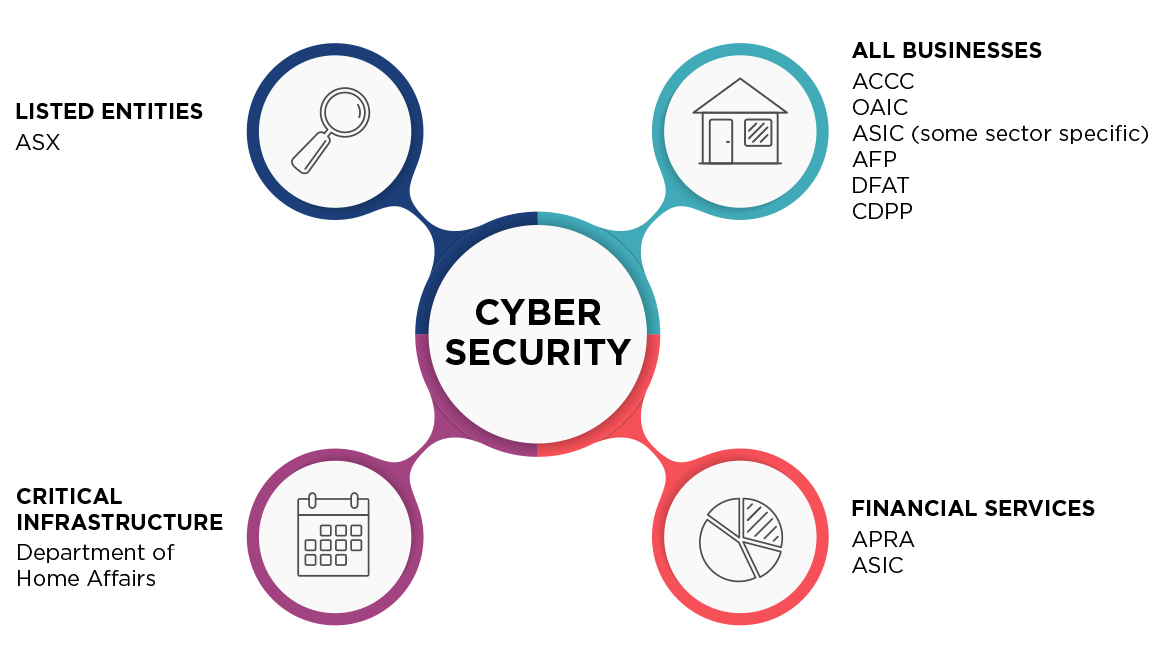
Set out below are Australia’s key regulators in the cyber security area, and the conduct they regulate.
All businesses
Australian Competition and Consumer Commission (ACCC)
- The ACCC can take enforcement action against businesses for engaging in misleading or deceptive conduct towards consumers (s 18, Australian Consumer Law (ACL)).
- In the cyber security context, businesses must ensure that any representations they make about the collection of consumer data and/or the cyber security characteristics of their products are accurate (s 29, 33-34, ACL)
Australian Securities and Investments Commission (ASIC)
- ASIC can take enforcement action against companies and directors if they breach their obligations under the Corporations Act 2001 (Cth).
- ASIC may commence proceedings against AFSL holders if they fail to put in place systems to prevent, detect and respond to cyber security incidents (s 912A, Corporations Act)
- ASIC may also take enforcement action where companies fail to comply with their continuous disclosure obligations, for example by failing to disclose cyber-attacks or data breaches (s 674, Corporations Act).
Office of the Australian Information Commissioner (OAIC)
- Organisations and agencies covered by the Privacy Act 1988 (Cth) must notify the OAIC and affected persons of any loss or unauthorised disclosure of personal information that is likely to result in serious harm (Privacy Act 1988 (Cth) pt IIIC).
- The Government has recently released an exposure draft of the Online Privacy Code, which will apply to social media organisations, data brokerage organisations, and large online platforms. The current proposal includes obligations to cease using or disclosing personal information on request, and greater protections for children and vulnerable groups. Submissions on the Online Privacy Bill are due by 6 December 2021.1
AFP, DFAT, CDPP
- Paying ransoms to hackers may breach a number of criminal laws if which may lead to investigation by the AFP and / or DFAT and possible prosecution.3
Australian Cyber Security Centre (ACSC)
- The ACSC’s voluntary guidelines represent best practice for complying with Australian cyber security standards.
- Further, a bill has been introduced earlier this year in June which would require public and private entities (other than small businesses) to report any ransomware payments to the ACSC.4
Critical Infrastructure
DEPARTMENT OF HOME AFFAIRS
- Operators of key national services may be given additional reporting and security requirements under proposed amendments to critical infrastructure laws.5
Financial Services
AUSTRALIAN PRUDENTIAL REGULATION AUTHORITY (APRA)
- APRA-regulated entities must comply with prudential standard CPS 234, which requires entities to clearly define IT security related roles and responsibilities, and maintain information security capability which is commensurate with the size and extent of threats to its IT assets, and maintain a compliant IT policy.
- APRA-regulated entities are also obliged to notify APRA of information security incidents and weaknesses shortly after becoming aware of them.
AUSTRALIAN SECURITIES AND INVESTMENTS COMMISSION (ASIC)
- ASIC can take enforcement action against companies and directors if they breach their obligations under the Corporations Act 2001 (Cth).
- ASIC may commence proceedings against AFSL holders if they fail to put in place systems to prevent, detect and respond to cyber security incidents (s 912A, Corporations Act)
- ASIC may also take enforcement action where companies fail to comply with their continuous disclosure obligations, for example by failing to disclose cyber-attacks or data breaches (s 674, Corporations Act).
Listed entities
AUSTRALIAN SECURITIES EXCHANGE (ASX)
- ASX listed entities must comply with their continuous disclosure obligations, by disclosing information that could materially affect the value of that company’s securities. This could relevantly include, for example, cyber-attacks or data breaches (ASX Listing Rule 3.1).
RECENT REGULATORY TRENDS
The number and scope of cyber security regulations is increasing
While there are already a significant number of regulations for Australian businesses to consider in the context of cyber security, the Commonwealth Government is considering further cyber specific regulations which are likely to increase the regulatory burden on Australian businesses.
This includes:
Cyber Security Strategy 2020: As we have previously noted, the Commonwealth Government is continuing its work on its Cyber Security Strategy 2020, through which it is considering introducing stronger cyber security regulations to make Australia more resilient to cyber security threats. This includes consideration of mandatory governance standards for large business, cyber security codes, mandatory standards for smart devices and standards requiring manufacturers and suppliers to disclose software vulnerabilities.
Critical infrastructure reforms
As we have previously discussed (see our briefings here and here), the Government is also in the process of amending the Security of Critical Infrastructure Act 2018.5 Under the proposed amendments, owners of key infrastructure assets will be required to:
- notify the Government of imminent cyber security incidents as soon as possible after becoming aware of them; and
- in the case of a serious incident, comply with an expansive range of directions given by the Minister for Home Affairs.
These powers will apply to a broader class of critical infrastructure, affecting assets in the aviation, banking, financial markets, food and groceries and telecommunications sectors.
Privacy Act
The Government’s review of the Privacy Act has led to a number of significant proposed reforms to privacy legislation, as outlined in an exposure draft6 and discussion paper,7 which are both currently open for submissions (see our briefing here). Some of these proposals would increase penalties for breaches under the Privacy Act. They would also increase the likelihood of enforcement action by the OAIC, as well as private individuals (including class actions arising from new direct rights of action or statutory torts).
Regulators are considering investigation and enforcement action following cyber incidents
Businesses that fail to understand their cyber security obligations are increasingly at risk of regulatory action. We are seeing a shift away from government and regulators viewing the attacked as the victim.
Regulators have taken enforcement action against businesses for cyber security-related breaches, including by commencing court proceedings and imposing fines. For example:
- ASIC commenced its first action alleging deficiencies in cyber security practices in the Federal Court of Australia against RI Advice, a financial services company. ASIC has alleged that RI Advice failed to take reasonable steps to manage a series of cyber security incidents, and breached s912A of the Corporations Act as a financial services licensee (see our briefing here).
- The ACCC commenced proceedings against an online health booking platform that disclosed personal information to insurance brokers without consumers’ consent, resulting in a $2.9 million fine.8 Soon after that, the ACCC prosecuted another tech company for misleading consumers about the collection, retention and use of consumers’ data.9 While these actions did not relate to cyber-attacks, they demonstrate that the ACCC is focused on misleading business practices which undermine the ability of consumers to make informed decisions regarding the use and collection of their personal data. This could extend to the nature of statements made about data security.
- The OAIC recently issued a determination against a multi-national company for failing to prevent unauthorised third parties from accessing its customers’ personal information in a cyber-attack.
So, what can businesses expect in the future?
FUTURE DIRECTIONS IN ENFORCEMENT
Expect more enforcement action
While it is early days in enforcement of cyber regulations, the regulators are making clear that with the increasing prevalence of cyber-attacks and the centrality of data, cyber security is a regulatory priority. This includes enforcement.
- The OAIC has voiced its support for stronger penalties for breaches of the Australian Privacy Principles, particularly for large multinational corporations.10
- The ACCC is well-positioned to prosecute businesses that misrepresent their cyber security posture to consumers. In 2020, the consumer regulator received a $27 million funding boost to address digital security issues.11
- ASIC has identified cyber threats and cyber security as a strategic priority for the 2021-2025 period. While ASIC has said it will continue to support improving the cyber resilience of its regulated population in line with the approach of the Government,12 the ASIC Commissioner has stated that they will litigate when necessary.13 ASIC intends to employ ‘decisive, deterrence-based enforcement action’ in order to mitigate cyber risks and maintain the integrity of the financial market.14
- APRA has said that it will take a ‘much more targeted approach to ensuring CPS 234 is being fully complied with, and holding boards and management accountable where it is not’.15
Expect Australia to follow overseas trends
An increased focus on the enforcement of cyber security obligations is not a uniquely Australian experience. Rather, the Government has made clear that it is looking overseas in its assessment of Australia’s cyber security strategy.16
It is therefore possible that Australia will see some of the following overseas cyber trends:
- Actions taken in relation to consumer harm: Enforcement action has been taken against companies that have misled users about a product’s level of security,17 and those providing services with security flaws.18
- Model cyber security regulation: The cyber security code being considered by the Government may be modelled on overseas examples. In Europe, for example, the General Data Protection Regulation imposes security requirements for data processing which must include technical and organisational measures appropriate to the risk involved if the data were to be accessed by unauthorised third parties.19
- Focus on cyber ransoms: In addition to 31 other countries, Australia has agreed to focus attention on cyber ransoms by increasing domestic law enforcement measures and sharing information with overseas regulators.20
Businesses can remain ahead of the curve by keeping an eye on comparable overseas regulators and enforcement action being taken.
What are some things that you can do to avoid being the target of enforcement action?
HOW TO MINIMISE THE RISK OF REGULATORY ENFORCEMENT ACTION
|
Know your legal obligations |
Recent trends in regulatory enforcement send a clear message: non-compliance has consequences. However, with the ever-increasing number of regulations, it is difficult for businesses to know their obligations.
Businesses should pay attention to the state of play in this rapidly changing field, and proactively seek advice from legal advisors and other experts if they are unsure about their obligations.
|
Understand best practice |
Against a backdrop of increasingly demanding regulation, it is fundamentally important that businesses understand best practice for IT security. However, this is not easy.
For example, in the RI Advice case, ASIC’s case was that RI Advice had to have all 68 documents that ASIC pleaded to be the baseline Cybersecurity Documentation and Controls necessary to adequately manage risk in respect of cybersecurity and cyber resilience for itself and across its AR network. RI Advice put on a strike out application in relation to this pleading, which was dismissed. While substantive consideration of ASIC’s case by the court is ongoing, it is clearly a complicated matrix for companies to have regard to, especially in circumstances where ASIC confirmed that it did not allege that the minimum cybersecurity requirements were mandated by any particular laws, regulations or industry standards.22
|
Take steps to minimise cyber risk and maximise operational resilience |
Given the risk of enforcement action, businesses must be proactive in preventing, detecting and managing cyber security risks. Cyber security is no longer just an issue for the IT department. Regulators have made clear that directors need to understand management’s view of cyber risks; the potential likelihood and impacts of risk events; and the steps taken to address the risks.23 Failure to do so could lead to significant enforcement actions in the event of a cyber-attack.






